The eHash Main Page
Contents
1 List of Hash Functions
On this page you can find a collection of existing hash functions.
Collection of Cryptographic Hash Functions
2 Notation and Definition
3 Generic Attacks on Hash Functions
4 Some How Tos
4.1 Working with maths and Tex
We can write "normal" latex equation by using the math class. For instance the following code
<math>
{\textbf x}_{t} = {\textbf f}({x}_{t-1},{u}_{t-1},{p}_{t-1})
</math>
is displayed as
<math> {\textbf x}_{t} = {\textbf f}({x}_{t-1},{u}_{t-1},{p}_{t-1}) </math>
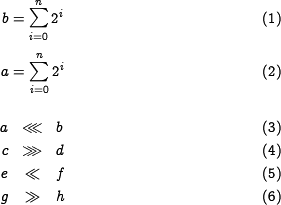
In order to use tex commands from the amsmath package we use the class amsmath. Automated numbering of equations works within a single amsmath environment. The class amsmath uses the tex template defined in /var/www/html/mediawiki/extensions/wikitex/wikitex.math.inc.tex
I changed the template such that we can define global commands. The template looks like
\documentclass[10pt]{article}
\usepackage{amssymb,amsmath,amscd,concmath}
% we can define whatever comments we would like to use for consistency.
% of course we have to somewhere list this special commands (may be we can use
% a pop up with editiing help or somkething similar
% for instance:
\newcommand{\rs}{\ensuremath{\gg}} %right shift >>
\newcommand{\ls}{\ensuremath{\ll}} %left shift <<
\newcommand{\rr}{\ensuremath{\ggg}} %right rotate >>>
\newcommand{\lr}{\ensuremath{\lll}} %left rotate <<<
\pagestyle{empty}
\begin{document}
%value%
\end{document}
For instance:
| code fragment | displayed equation |
|---|---|
<amsmath>
\begin{equation}
a = \sum_{i=0}^{n}{2^i}
\end{equation}
</amsmath>
|
|
| %value% in tex-template is \begin{equation}...\end{equation} | |
If we start a new amsmath environment then the equation numbering starts from counter=1 again. Start a new amsmath environment:
as we see both envrionments start with 1.
Note: so far I have no idea how to refer to an equation <math>\dots</math>
5 Getting started
ECRYPT is a Network of Excellence within the Information Societies Technology (IST) Programme of the European Commission. The information on this web site is provided as is, and no guarantee or warranty is given or implied that the information is fit for any particular purpose. The user thereof uses the information at his or her sole risk and liability.