SHA-1
From The ECRYPT Hash Function Website
Contents
1 General Description
SHA-1 is an iterated hash function.
1.1 Compression Function
The compression function takes as input a 512-bit message block and a 160-bit chaining variable, and produces a 160-bit chaining value. The compression function is described as follows:
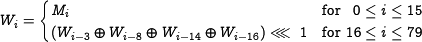
1.1.1 Message Expansion
The message expansion is defined as follows:
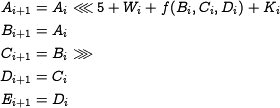
1.1.2 State Update Transformation
1.2 Padding Method
1.3 Constantsand Initial Value
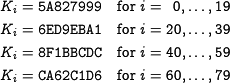
1.3.1 Constants
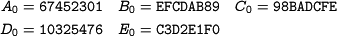
1.3.2 Initial Value
2 Claimed/Expected Security Margins
3 Security Anaylsis
- Best know attack:
 by Wang et.al.
by Wang et.al. - Best known collision example: 64-step collision by De Canniere and Rechberger
something like: best know attack to date: kind of attack, which variant has been looked at (e.g. round-reduced), complexity, and reference to paper and abstract.
may be make here a new page with the other cryptanalysis results.