Difference between revisions of "SHA-1"
From The ECRYPT Hash Function Website
(→State Update Transformation) |
(→State Update Transformation) |
||
| Line 9: | Line 9: | ||
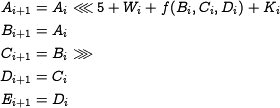
==== State Update Transformation ==== | ==== State Update Transformation ==== | ||
<amsmath> | <amsmath> | ||
| + | \begin{equation*} | ||
\begin{aligned} | \begin{aligned} | ||
| − | A_{i+1} &= A_i \ | + | A_{i+1} &= A_i \lr 5 + W_i + f(B_i,C_i,D_i) + K_i\\ |
B_{i+1} &= A_i\\ | B_{i+1} &= A_i\\ | ||
| − | C_{i+1} &= B_i | + | C_{i+1} &= B_i \rr \\ |
D_{i+1} &= C_i\\ | D_{i+1} &= C_i\\ | ||
E_{i+1} &= D_i | E_{i+1} &= D_i | ||
\end{aligned} | \end{aligned} | ||
| + | \end{equation*} | ||
</amsmath> | </amsmath> | ||
Revision as of 10:37, 12 October 2006
Contents
1 General Description
SHA-1 is an iterated hash function.
1.1 Compression Function
The compression function takes as input a 512-bit message block and a 160-bit chaining variable, and produces a 160-bit chaining value. The compression function is described as follows:
1.1.1 Message Expansion
1.1.2 State Update Transformation
1.2 Padding Method
1.3 Initial Value and Constants
WikiTeX: latex reported a failure, namely:
/data/www/ehash/html/extensions/wikitex/wikitex.sh: line 59: latex: command not found
2 Claimed Security Margins
3 Security Anaylsis
- Best know attack: <math>2^{63}</math> by Wang et.al.
- Best known collision example: 64-step collision by De Canniere and Rechberger
something like: best know attack to date: kind of attack, which variant has been looked at (e.g. round-reduced), complexity, and reference to paper and abstract.
may be make here a new page with the other cryptanalysis results.